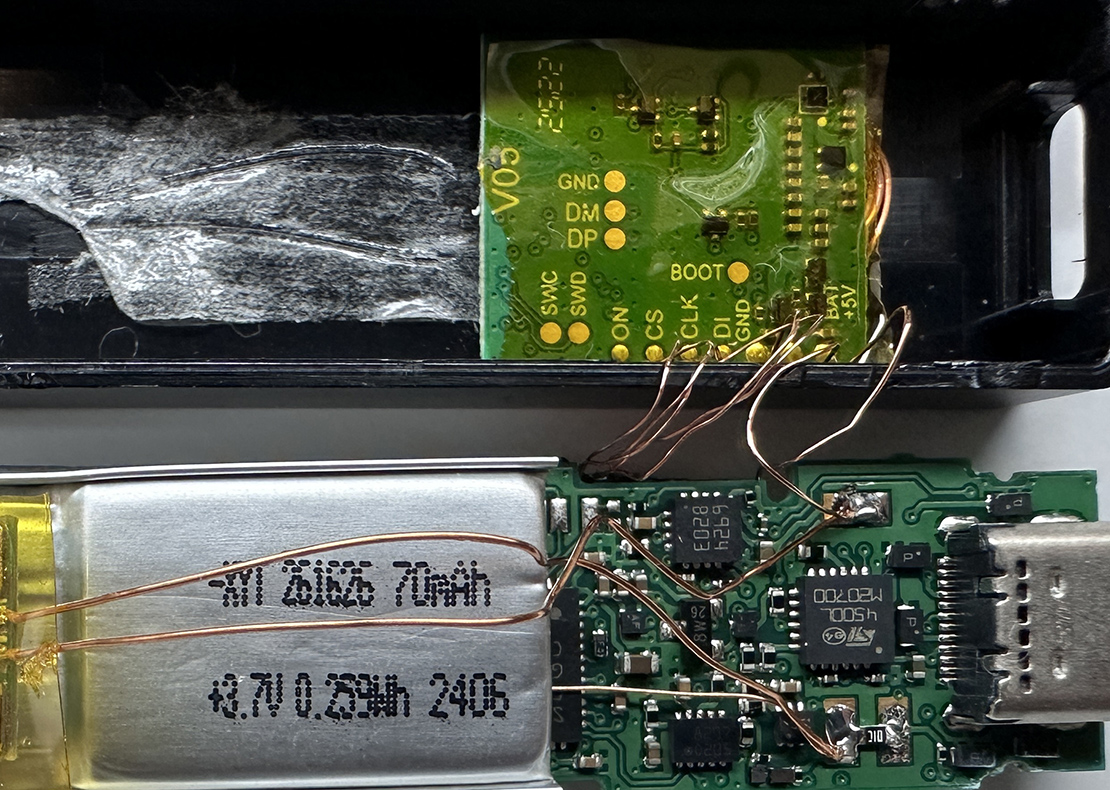
Reverse Engineering a Ledger Nano X Hardware Implant
Hardware espionage involves intentionally compromising the integrity or modifying the functionality of an electronic product in a way that is beneficial to the attacker. Techniques like supply chain attacks and hardware implants are often discussed, but rarely seen in the wild.
In this presentation, Joe explores the history of hardware espionage and details his reverse engineering process of a real-world hardware implant discovered inside of a Ledger Nano X cryptocurrency hardware wallet.
Documentation
- Slides: Reverse Engineering a Ledger Nano X Hardware Implant (Revised May 29, 2026)