Palm OS Password Retrieval and Decoding
Palm OS devices offer a built-in Security application which is used for the legitimate user to protect and hide records from unauthorized users by means of a password. In all basic built-in applications (Address, Date Book, Memo Pad, and To Do List), individual records can be marked as "Private" and will only be accessible if the correct password is entered. It is possible to obtain an encoded form of the password, determine the actual password due to a weak, reversible encoding scheme, and access a user's private data. In order for this attack to be successful, the attacker must have physical access to the target Palm device.
Application: Palm OS 3.5.2 and earlier
Platforms: All Palm OS Platform Devices
Severity: Passwords can easily be obtained and decoded allowing an attacker to access all private records on a Palm device.
Security Advisory: Palm OS Password Retrieval and Decoding (CVE-2000-1008)
PalmCrypt demonstrates the weak encoding scheme used to obfuscate the Palm system password in devices running Palm OS 3.5.2 and earlier. This tool converts an encoded password block to an ASCII password and vice versa.
Platforms: Win 95/98/NT/2K
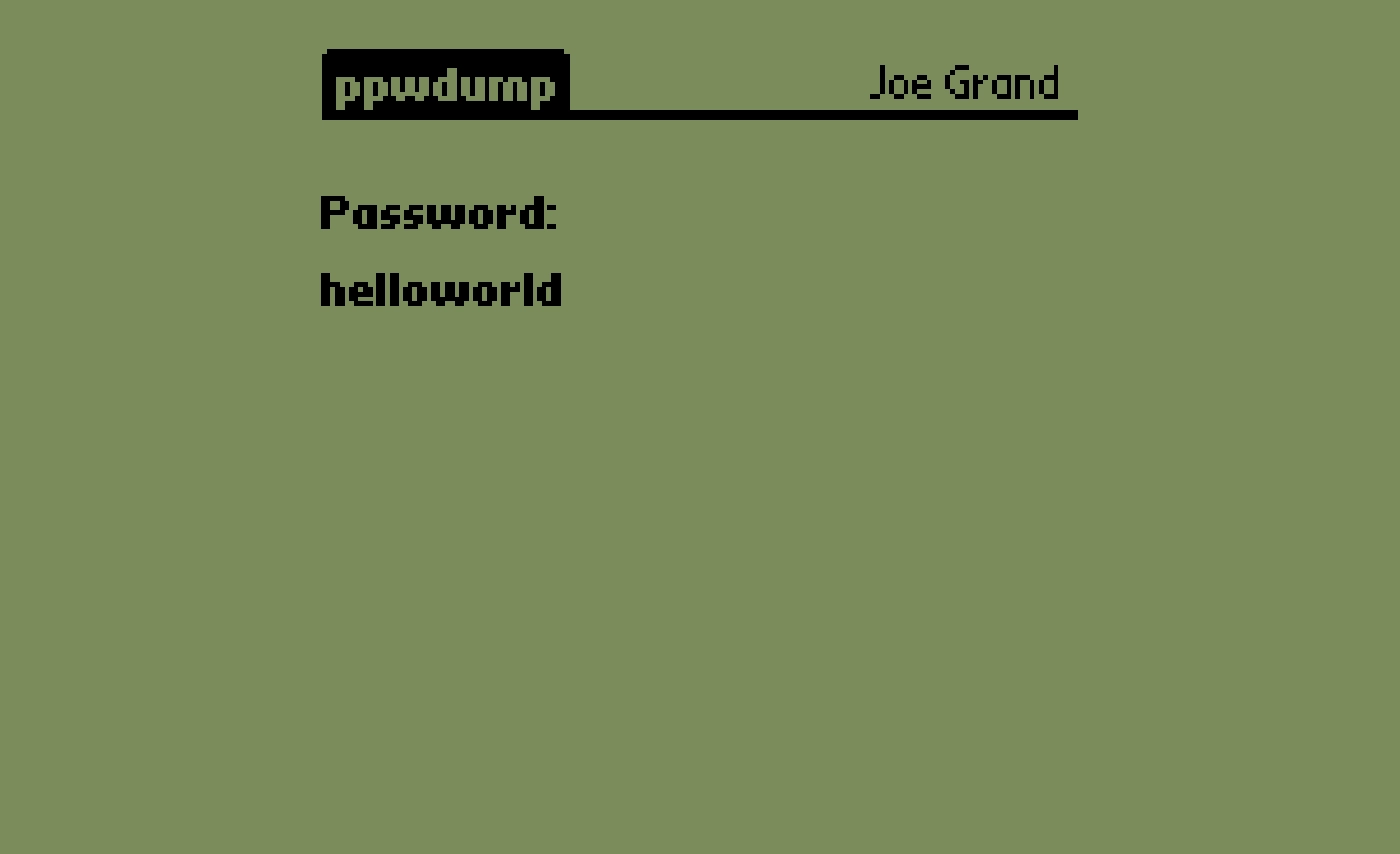
ppwdump is a system password recovery tool for Palm devices. It obtains the "Unsaved Preferences" database from the local device (where the encoded system password is stored) and decodes the password to its original ASCII equivalent.
Platforms: Palm OS 3.5.2 and earlier
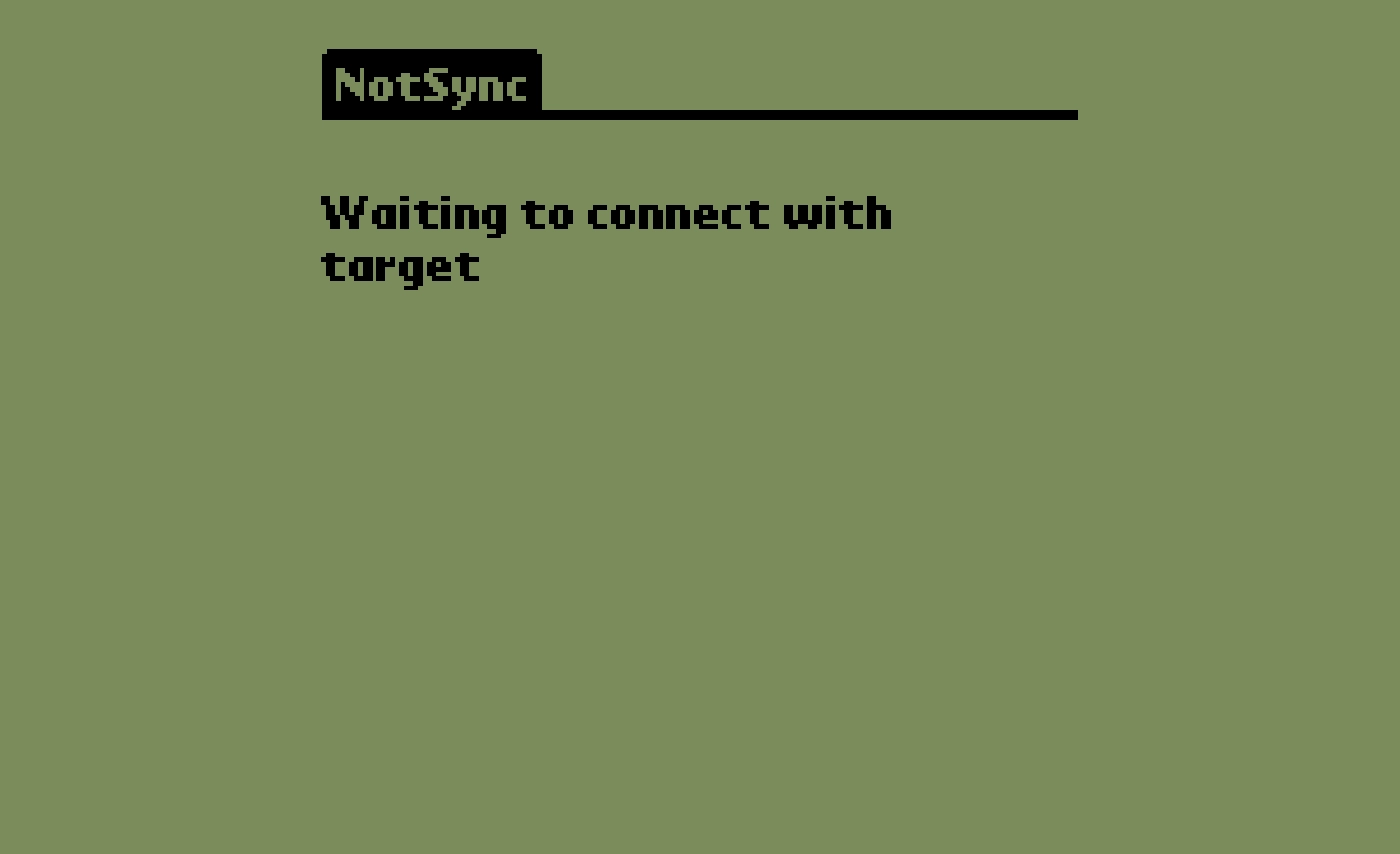
NotSync demonstrates the simplicity of obtaining and decoding the Palm system password. This tool imitates the initial stages of the HotSync process via the infrared (IR) port and retrieves and decodes the password of the target device.
Platforms: Palm OS 3.3 and greate
Originally published on the @stake website.