An Overview of Hardware-Based Covert Channels
Covert channels are methods of surreptitious data transfer used to communicate with or exfiltrate information from a compromised computer system. They can exist within any layer of the system, including hardware, application software, operating system, or network stack. Typically, covert channels are employed on critical, protected, and/or air-gapped assets that an attacker may not be able to access by conventional means.
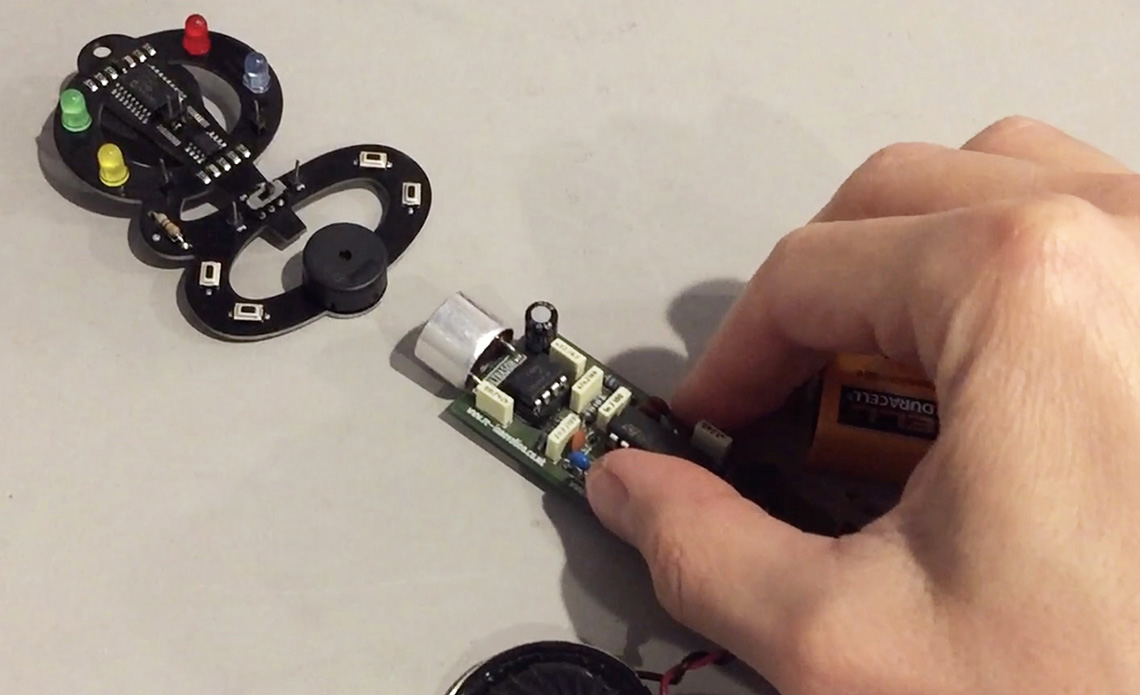
This presentation provides an overview of hardware-based covert channels and demonstrates a few techniques that can be easily implemented with off-the-shelf electronics.
- Slides: Setec Astronomy: An Overview of Hardware-Based Covert Channels
- Video: Setec Astronomy: An Overview of Hardware-Based Covert Channels (RoadSec@Home 2020) (YouTube)